Presumably, by now you’ve heard about the Heartbleed Bug that was discovered last week. You know, the one where we found out that a whole lot of the internet wasn’t as safe as we’d thought. Mr. Napping came home the day it was discovered and described it to me in all the technical and geeky terms he could think of. One of his friends at work had spent a lot of the day patching their servers and the two of them had commiserated the problem while getting their ‘geek high’ at the same time. I got the residual effects of the high and a whole lot of computer jargon I didn’t completely understand. While I understood the basics of what he was saying, the magnitude of the issue didn’t really hit home at that point. So, if you’re still a little confused about just what the issue is, let me see if I can break it down for you.
Basically, there was a problem with OpenSSL. This is the open source (anyone can use it) software that a lot of sites use to transfer encrypted information – like passwords. There was a flaw in the software that would leak some of the data, now decrypted. The data being returned could vary from passwords and credit card numbers to the actual key used to decrypt the data. This would allow hackers to grab small pieces of information from transfers without detection. After enough of these small grabs, they would eventually have the code needed to decipher all the information and could decode any and all transfers encrypted with OpenSSL. And this has been possible for the past two years. Plenty of time to do some major damage. And it was undetectable. Make sense? See why the entire tech community was hysterical? Think of all the encrypted information you send… passwords, credit card numbers, bank information, personal identification numbers… not really stuff you want just anyone to have access to, am I right? So, now what?
Well, the good news is that the problem was discovered by a Google security team employee and a software firm, not hackers and bad guys with terrible intentions. There’s no evidence this was a known issue to anyone before the discovery last Monday; meaning even though the information could have been stolen, it probably wasn’t. The bad news is there’s not a lot you can do if your info has been snagged already. Keep a watch on your accounts (bank, email, social media, and the like) for any unauthorized use and report it immediately.
To prevent any further problems, though, there are things you can do. First off, find out what sites you use were effected by the issue. There is a gigantic list of websites HERE you can scan through and see if any of the ones you use were affected. Don’t want to go through all that (can’t blame you there!), Mashable put together this list of popular websites and their vulnerability. They also have other articles that can help you understand Heartbleed and what to do now. The Mashable list will tell you the passwords you need to change now to make your accounts as secure as possible. Still have questions about a particular site? You can use LastPass’ “Heartbleed Checker” to check individual https:// urls and their vulnerability. And, if you use LastPass, you can click on the security check in your vault and it will tell you what sites were vulnerable and give you suggestions on what to do now. I’m thinking I’d rather be safe than sorry (and I should have changed my passwords probably three times since I last did), so I’m just going to change all my passwords.
Bloggers, (well, everyone actually, but bloggers especially) should change all social media site passwords. Picmonkey is a site commonly used by bloggers for photo editing. It was vulnerable. Change that password. Etsy was vulnerable. Yahoo, Imgur, Flickr, Madmimi, Dropbox, Copy, a large majority of online retailers, 1001 Free Fonts, weather.gov, ucsd.edu… all were vulnerable. There isn’t a safe “type” of website out there. And, just because your banking site was safe doesn’t mean your info couldn’t have been pulled from somewhere else. If you entered credit card info on a site that was vulnerable, so was your information. So, be careful and keep a close eye on your accounts. All of them.
Other common sites bloggers use often could have been affected. Several advertising and media sites (Social Fabric, Pollinate, the IZEA network, Clever, Mom it Forward, Collective Bias, and Klout to name a few) may have been affected. Some of those sites have applied patches and some have not. Changing your passwords is probably the safest thing to do. If there are sites that share passwords (yeah, the big naughty no-no we all do), change the other site’s password too. Pollinate was one of the sites they aren’t sure is safe yet. They haven’t updated their SSL certificate yet so they may still be running a vulnerable version of the software. If your Pollinate account was hit and had the same password as your bank account, the hackers now have your bank account password as well, even though most banking sites weren’t affected. If you change your Pollinate account password, there is still a chance your information can be stolen until they update their SSL version and it’s certificate and a confirmed patch is announced.
(Side note: most banking sites were not hit by the Heartbleed bug, however, you should check with your financial institution for confirmation. Our Wells Fargo accounts weren’t vulnerable, but my USAA accounts could have been. Double check to make sure your bank wasn’t one that was vulnerable.)
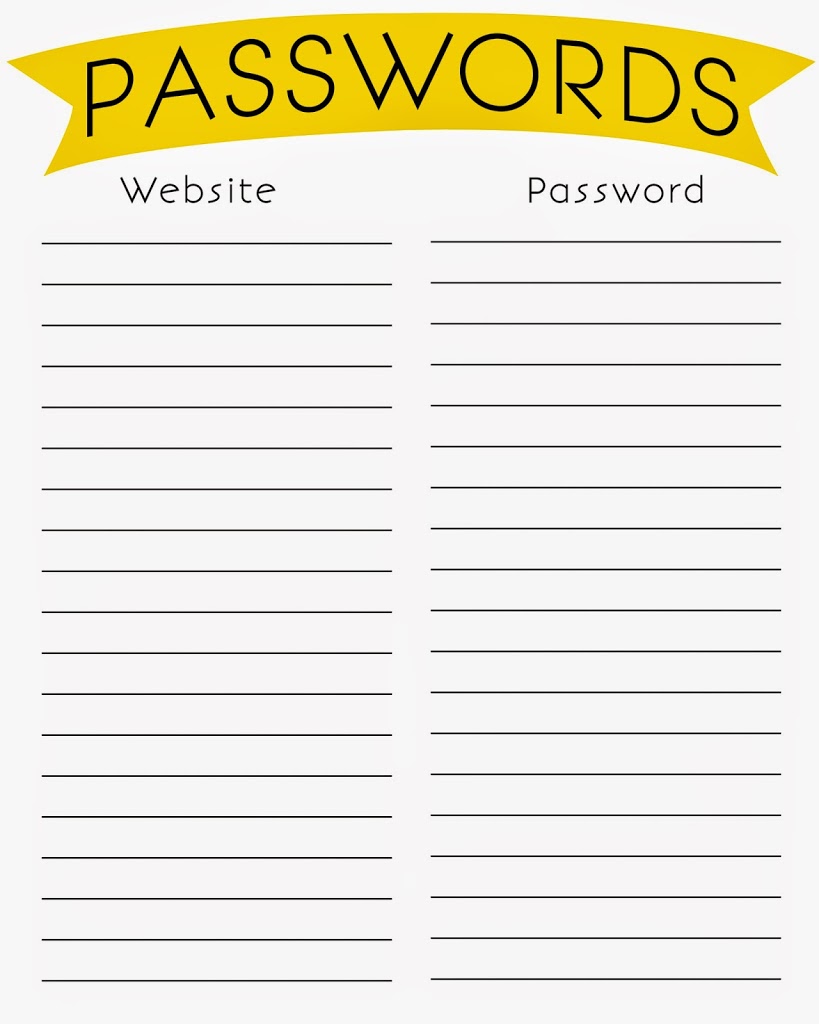
Looks like we’ve got a lot of passwords to change… and to make it easier to keep track of all these new passwords, here are a couple printables for you to use. Right click, open in a new tab or window. The right click the image again and “save as” the image to your computer. You can then print from there. Feel free to print as many copies as you want/need. Please do not post these files on your own blog, other pages or share via email. If you would like to share the printable, send your family and friends to this post, where they can download their own copies. Thanks! The white background allows the pages to be printed on any paper, including colored papers.